Adex’s investigation into XCSSET began with an iOS development studio concerned that its macOS infrastructure may have been exposed to malware. What followed was a case study in how a developer workstation can become part of a wider supply-chain infection without any obvious sign to the person using it.
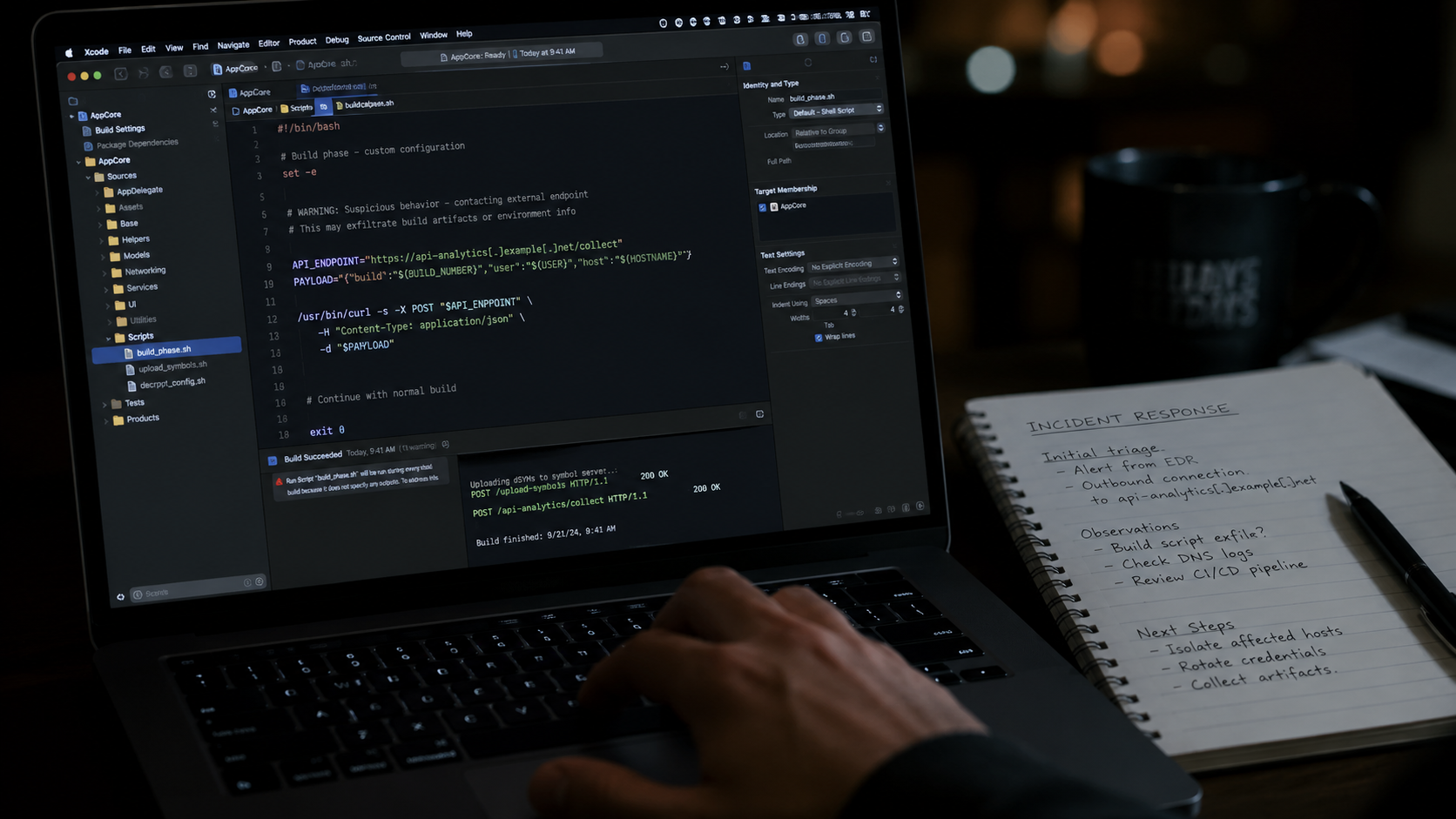
XCSSET is a modular macOS malware family first documented in 2020. Its distribution method is unusual because it does not need to appear inside the final app. Instead, it hides inside Xcode project files, particularly project.pbxproj, where build instructions are stored. When a developer opens a compromised Xcode project and builds it, the malicious script can run as part of the normal development process.
That makes the risk different from a typical infected download. The target is the developer workflow itself: repositories, build scripts, shared projects, third-party SDKs, and machines used to produce iOS or macOS applications.
What Adex Found on the Workstation
The first visible sign was a repeated process: osascript /tmp/jl, followed by a large base64-like argument. osascript is Apple’s built-in AppleScript interpreter, so its presence alone is not suspicious. But repeated execution from /tmp, a temporary directory, raised concern.
The file /tmp/jl appeared and vanished too quickly to inspect manually. Adex captured it using a simple polling loop that copied the file every 100 milliseconds when it appeared. Once preserved, the file was identified as a compiled AppleScript in binary .scpt format.
Further analysis showed layers of obfuscation. The AppleScript extracted and decoded packed base64 payloads, then executed a shell script. That script collected details about the system, including username, locale, macOS version, CPU architecture, System Integrity Protection status, Mac serial number, Chrome extension manifests, and Chrome binary information. The data was then sent through a curl request to https://riggletoy.ru/l.
How the Malware Persisted
The investigation found that the infection was not limited to one script. Adex traced persistence to a fake Launchpad.app placed in a user cache directory: ~/Library/Caches/jaq.kuugp.dirzpf/Launchpad.app. The legitimate Launchpad application is located at /System/Applications/Launchpad.app, which is protected by Apple’s System Integrity Protection.
This fake application matched a persistence method documented in 2025, where malware rewrites the Dock entry so that clicking Launchpad opens both the real application and the malicious component. To the user, nothing appears different on screen.
The workstation had more than 20 modified Xcode projects. Adex reported that the files were changed within the same minute, pointing to automated propagation across the home directory rather than manual edits. That detail is central to the case: once active, XCSSET can scan for other Xcode projects and inject itself into them, turning one infected machine into a distribution point.
Why Project Cleanup Alone Fails
A key finding from the investigation is that cleaning infected Xcode projects before removing persistence can lead to reinfection. The malware’s staying power comes from autostart mechanisms, shell profile injections, launch agents, rogue applications, and git hooks.
Adex’s recommended remediation order is specific: remove persistence points first, reboot the machine, then restore Xcode projects from a known-clean git state. Reversing that sequence leaves the active mechanism in place while defenders repair the files it can modify again.
The report also advises developers to inspect Xcode build phases before building unfamiliar projects. Since project.pbxproj files can be opened as plain text, developers can review them before executing anything in Xcode. Other suggested checks include scanning for suspicious use of curl, osascript, base64, /tmp/, launch agents, and global git hook paths.
The GitHub Link
Adex extended the investigation beyond the infected workstation and searched public GitHub repositories. The team reported 24 repositories containing XCSSET payload chains. Examples included PrinceMittal1/DemoForAuthFlow, zzzznick/dummy-ios, and dvillegastech/ReaxBD.
Several repositories showed recent activity. The report highlighted usamajaved357/Breezy, a SwiftUI weather project committed in March 2026, because it used the same riggletoy.ru domain found in the live workstation sample. Another repository, xiaoyouPrince/XYDevTool, used netcdndev.in, which Adex said was not present in public indicator lists at the time of the investigation.
The findings suggest that XCSSET remains active in developer spaces where project files are often trusted by default. Its technical success depends less on advanced evasion than on a basic habit: developers routinely share, clone, and build project files they have not fully read. For teams building Apple software, Adex’s investigation shows that build files now need the same scrutiny as source code, dependencies, and credentials.